
The Coruna exploit kit is an evolution of the framework used in the Operation Triangulation espionage campaign, which in 2023 targeted iPhones via zero-click iMessage exploits.
The software has been expanded to target modern hardware, specifically including Apple’s A17 and M3 chips, as well as operating systems up to iOS 17.2.
Coruna contains five full iOS exploit chains leveraging 23 vulnerabilities, among them CVE-2023-32434 and CVE-2023-38606 also used in Operation Triangulation.
After analyzing the exploit code for the two security issues, Kaspersky researchers determined that Coruna ran an updated version of the exploit used in Operation Triangulation that had started since 2019.
Additional code similarities led to the conclusion that the kit is the successor to the malicious framework leveraged in the Triangulation campaign that also targeted iPhones on Kaspersky’s network.
“During our analysis we’ve discovered that the kernel exploit for CVE-2023-32434 and CVE-2023-38606 vulnerabilities used in Coruna, in fact, is an updated version of the same exploit that was used in Operation Triangulation,” the researchers say in a report today.
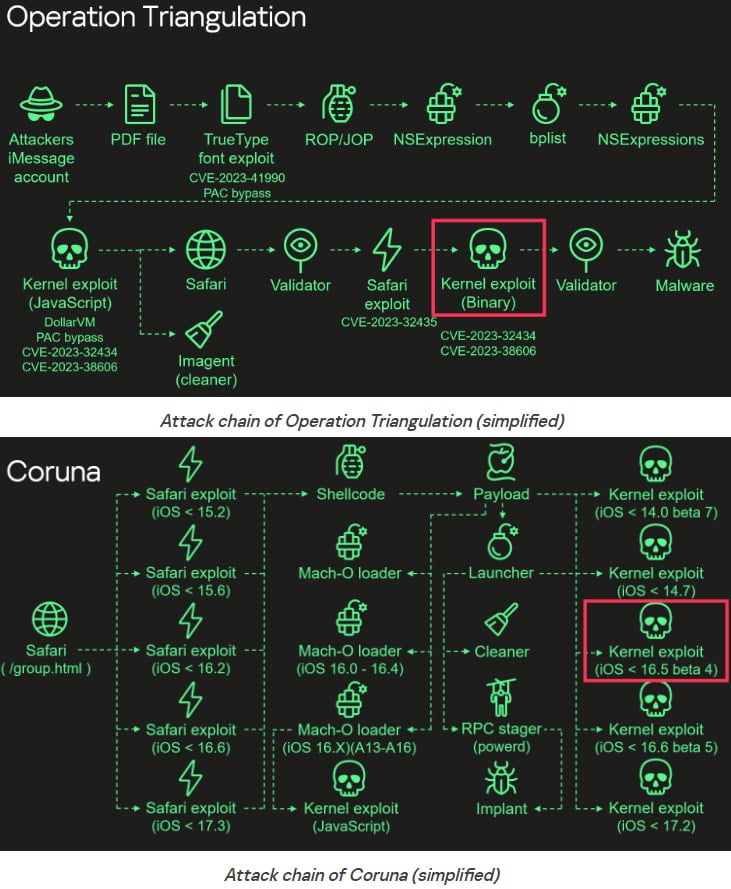
Kaspersky’s analysis shows that the attack begins in Safari with a stager that fingerprints the device, selects suitable RCE and PAC exploits, and then retrieves encrypted metadata for subsequent stages.
The payload downloads additional encrypted components, decrypts them using ChaCha20, decompresses them with LZMA, and parses custom container formats to obtain package information.
Based on the device’s architecture and iOS version, it selects and executes the appropriate kernel exploit, Mach-O loader, and launcher to deploy the spyware implant.
Kaspersky’s findings indicate that the payloads support targeting ARM64 and ARM64E architectures, with explicit checks for A17, M3, M3 Pro, and M3 Max chips.
Also, the package IDs and system checks indicate that the exploits can target:
- iOS < 14.0 beta 7
- iOS < 14.7
- iOS < 16.5 beta 4
- iOS < 16.6 beta 5
- iOS < 17.2
Boris Larin, principal security researcher at Kaspersky Global Research and Analysis Team (GReAT), says the connection with Triangulation became evident after analyzing Coruna’s binaries.
“Coruna is not a patchwork of public exploits; it is a continuously maintained evolution of the original Operation Triangulation framework.”
Additionally, the developers continued to update the framework by including checks for newer processors (e.g., M3) and iOS builds.
Since Coruna has also been used in financially-motivated campaigns aiming to steal cryptocurrency via fake exchange websites, Larin notes that “what began as a precision espionage tool is now deployed indiscriminately.”
Operation Triangulation was a highly sophisticated iOS espionage campaign that used multiple zero-day exploits to silently infect iPhones and deploy spyware implants.
It was discovered by Kaspersky during internal WiFi network monitoring in June 2023, though the campaign had started four years earlier.
In late 2023, the same researchers found that these attacks leveraged undocumented features in Apple chips to bypass hardware-based security protections.
Another exploit kit, dubbed DarkSword, was disclosed earlier this month by researchers at mobile security companies Lookout and iVerify, and Google.
Like Coruna, DarkSword is being used by multiple threat actors, but all appear to be leveraging it for espionage operations. It should be noted that DarkSword is now publicly available, which increases the risk of cybercriminals starting to leverage it against unpatched iPhones.
Apple has published a bulletin to address all these recently uncovered exploit kits, noting that fixes for all flaws have been made available via security updates for the latest, as well as earlier, iOS versions.

