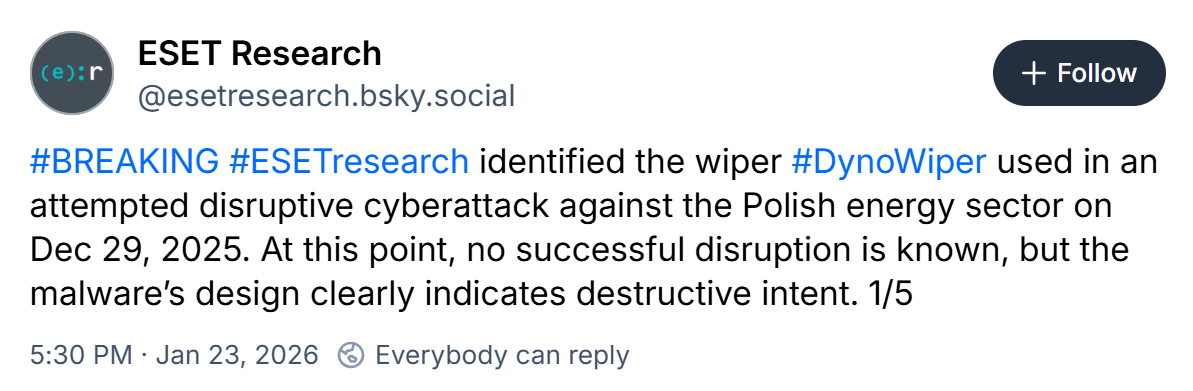
The attack involved data-wiping malware that ESET researchers have now analyzed and named DynoWiper
23 Jan 2026
•
,
1 min. read

In late 2025, Poland’s energy system faced what has been described as the “largest cyberattack” targeting the country in years. ESET Research has now found that the attack was the work of the notorious Russia-aligned APT group Sandworm.
“Based on our analysis of the malware and associated TTPs, we attribute the attack to the Russia-aligned Sandworm APT with medium confidence due to a strong overlap with numerous previous Sandworm wiper activity we analyzed,” said ESET researchers. “We’re not aware of any successful disruption occurring as a result of this attack,” they added.
While details regarding the intended impact continue to be investigated, ESET researchers have highlighted the fact that the coordinated attack occurred on the 10th anniversary of the Sandworm-orchestrated attack against the Ukrainian power grid, which resulted in the first ever malware-facilitated blackout. Back in December 2015, Sandworm used the BlackEnergy malware to gain access to critical systems at several electrical substations, leaving around 230,000 people without electricity for several hours.
Fast forward a decade and Sandworm continues to target entities operating in various critical infrastructure sectors, especially in Ukraine. In their latest APT Activity Report, covering April to September 2025, ESET researchers noted that they spotted Sandworm conducting wiper attacks against targets in Ukraine on a regular basis.
For any inquiries about our research published on WeLiveSecurity, please contact us at threatintel@eset.com.ESET Research offers private APT intelligence reports and data feeds. For any inquiries about this service, visit the ESET Threat Intelligence page.
IoCs
| SHA-1 | Detection | Description |
| 4EC3C90846AF6B79EE1A5188EEFA3FD21F6D4CF6 | Win32/KillFiles.NMO | DynoWiper. |


