
A new sample of the ToneShell backdoor, typically seen in Chinese cyberespionage campaigns, has been delivered through a kernel-mode loader in attacks against government organizations.
The backdoor has been attributed to the Mustang Panda group, also known as HoneyMyte or Bronze President, that usually targets government agencies, NGOs, think tanks, and other high-profile organizations worldwide.
Security researchers at Kaspersky analyzed a malicious file driver found on computer systems in Asia and discovered that it has been used in campaigns since at least February 2025 against government organizations in Myanmar, Thailand, and other Asian countries.
Evidence showed that the compromised entities had prior infections with older ToneShell variants, PlugX malware, or the ToneDisk USB worm, also attributed to state-sponsored Chinese hackers.
New kernel-mode rootkit
According to Kaspersky, the new ToneShell backdoor was deployed by a mini-filter driver named ProjectConfiguration.sys and signed with a stolen or leaked certificate valid between 2012 and 2015 and issued to Guangzhou Kingteller Technology Co., Ltd.
Mini-filters are kernel-mode drivers that plug into the Windows file-system I/O stack and can inspect, modify, or block file operations. Security software, encryption tools, and backup utilities typically use them.
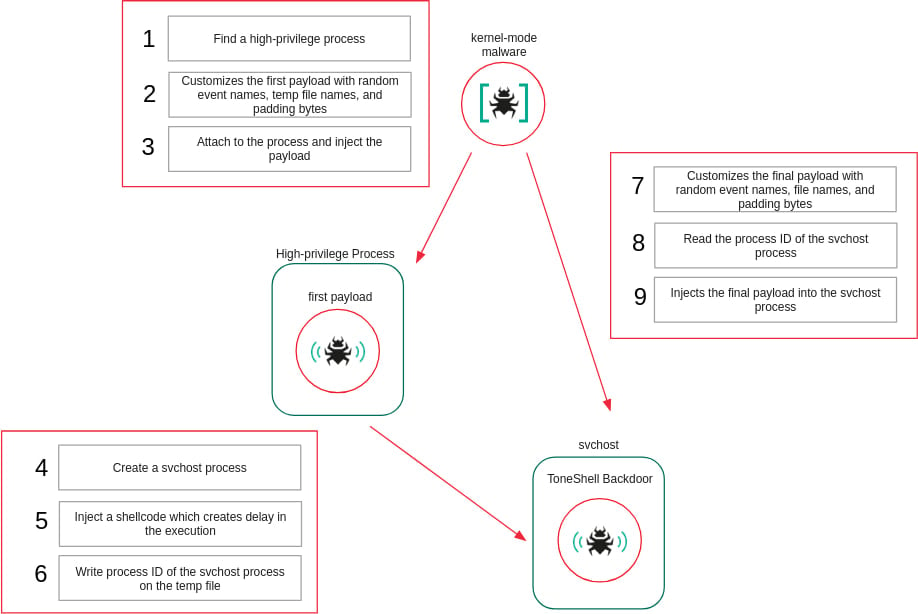
ProjectConfiguration.sys embeds two user-mode shellcodes in its .data section, each executed as a separate user-mode thread to be injected into user-mode processes.
To evade static analysis, the driver resolves required kernel APIs at runtime by enumerating loaded kernel modules and matching function hashes, rather than importing functions directly.
It registers as a mini-filter driver and intercepts file-system operations related to deletion and renaming. When such operations target the driver itself, they are blocked by forcing the request to fail.
The driver also protects its service-related registry keys by registering a registry callback and denying attempts to create or open them. To ensure priority over security products, it selects a mini-filter altitude above the antivirus-reserved range.
Additionally, the rootkit interferes with Microsoft Defender by modifying the configuration of the WdFilter driver so it is not loaded into the I/O stack.
To shield injected user-mode payloads, the driver maintains a list of protected process IDs, denies handle access to those processes while the payloads are executing, and removes protection once execution completes.
“This is the first time we’ve seen ToneShell delivered through a kernel-mode loader, giving it protection from user-mode monitoring and benefiting from the rootkit capabilities of the driver that hides its activity from security tools,” says Kaspersky.
Source: Kaspersky
New ToneShell variant
The new variant of the ToneShell backdoor that Kaspersky analyzed features changes and stealth enhancements. The malware now uses a new host identification scheme based on a 4-byte host ID market instead of the 16-byte GUID used previously, and also applies network traffic obfuscation with fake TLS headers.
In terms of the supported remote operations, the backdoor now supports the following commands:
- 0x1 — Create a temporary file for incoming data
- 0x2 / 0x3 — Download file
- 0x4 — Cancel download
- 0x7 — Establish a remote shell via a pipe
- 0x8 — Receive operator command
- 0x9 — Terminate shell
- 0xA / 0xB — Upload file
- 0xC — Cancel upload
- 0xD — Close connection
Kaspersky advises that memory forensics is key in uncovering ToneShell infections backed by the new kernel-mode injector.
The researchers have high confidence in attributing the new ToneShell backdoor sample to the Mustang Panda cyberespionage group. They assess that the threat actor has evolved its tactics, techniques, and procedures to gain operational stealth and resilience.
The cybersecurity company provides in its report a short list of indicators of compromise (IoCs) to help organizations detect Mustang Panda intrusions and defend against them.


