Here’s how open-source intelligence helps trace your digital footprint and uncover your weak points, plus a few essential tools to connect the dots
20 Nov 2025
•
,
5 min. read

Whatever the reason, we spend vast amounts of time online, tapping into the untold expanse of information, communication and resources. Sometimes, the challenge isn’t finding some data, but knowing what’s relevant, real and worth trusting. Anyone working with information needs to be able to cut through the noise and discern the authenticity of the data, which requires being methodical and deliberate when choosing and using our sources – and having the right tools to expedite the process.
And this is where OSINT comes in. Short for “Open Source Intelligence”, OSINT refers to the gathering and analysis of publicly available data to produce actionable insights. Journalists can use it for investigations and fact-checking. Businesses can rely on it for tracking their reputation or monitor competitors. Researchers can leverage it for their studies. Basically, if you’re trying to make sense of public data, you’re already in OSINT territory. Needless to say, OSINT has use cases in cybersecurity, too.
OSINT in cybersecurity
What started as a practice for military and law enforcement purposes has become an important discipline in cybersecurity, enabling security practitioners to gauge risks, spot exposed assets and understand potential threats. The benefits are obvious: OSINT gives organizations a clearer picture of their digital footprint and helps them spot their weak spots before they can be exploited for bad ends.
For example, pentesters can use it during reconnaissance to locate exposed domains or services. Threat intelligence teams can rely on it to follow malicious activity on social media or underground forums. Meanwhiie, red and blue teams can both use OSINT to test how visible their infrastructure is from the outside. It also allows security professionals to complement their understanding of bad actors by spotting their tactics and watching their chatter.
Of course, the same techniques work both ways. Every piece of information about an organization that’s publicly accessible is equally available to adversaries, who can leverage OSINT for spearphishing attacks, among other things, as knowing a target’s habits or coworkers makes the bait more convincing.
Tools and techniques
OSINT practitioners can use a plethora of open-source and proprietary tools that automate data collection and analysis. Some of the most common ones are:
- Shodan and Censys: these are staples among search engines for internet-connected devices, such as routers and IP cameras. They help you see what’s publicly exposed and shouldn’t be, such as open ports, exposed APIs and insecure certificates, which helps identify exposed systems in an organization’s network.
- Maltego: a visual mapping tool to link people, domains, and IPs to reveal hidden connections.
- TheHarvester, Recon-ng, SpiderFoot: sets of scripts that collect email addresses, subdomains, hosts, usernames, etc., from multiple sources (such as WHOIS, search engines, social media sites and public databases). They come in handy in the reconnaissance phase of penetration testing attacks.
- OSINT Framework and OSINTCombine: these tools organize hundreds of free resources by category (web search, social media platforms, government sites, etc.), making it easy for both newcomers and seasoned analysts to find the right tool for each task.
- Google Dorks and GooFuzz: advanced search techniques (using operators like site: or filetype:) that help uncover sensitive data indexed by search engines.
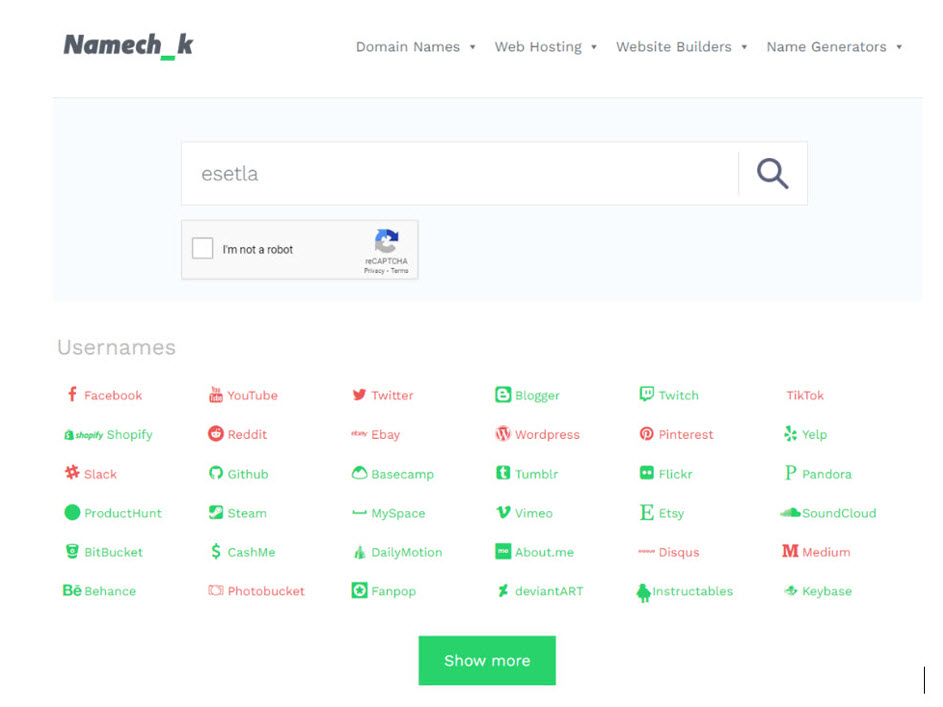
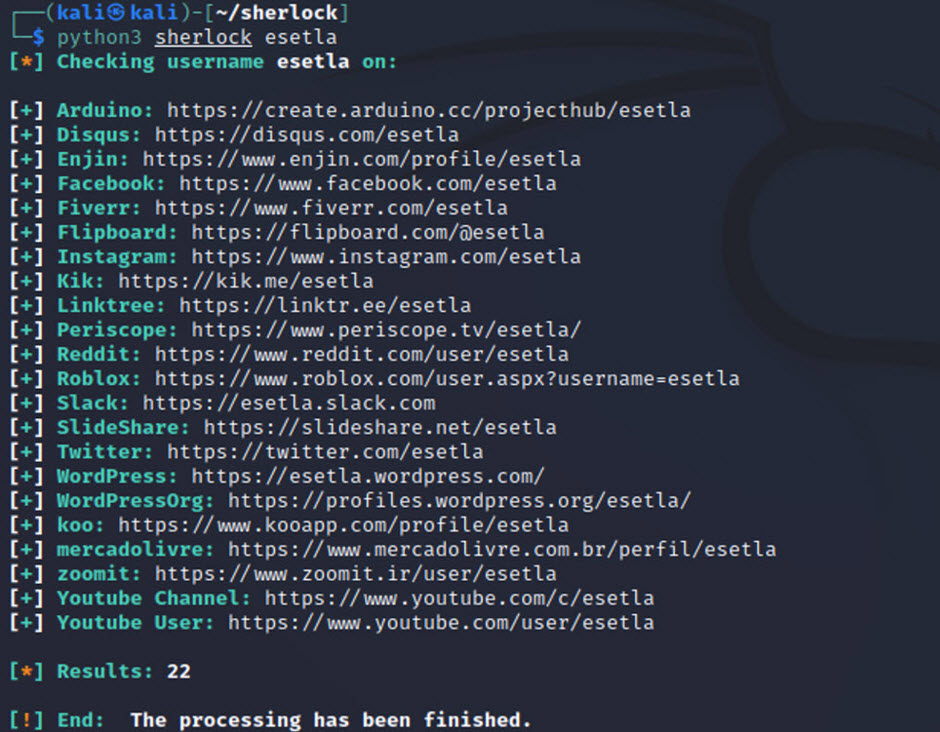
- Social media tools: platforms like Namechk and Sherlock check whether a username exists across dozens of sites and are, therefore, useful for building digital profiles. More advanced tools such as Skopenow, Telegago, or AccountAnalysis analyze behavior and connections on platforms like X, Facebook, or Telegram.
- Metadata analysis: tools such as ExifTool, FOCA, and Metagoofil extract geolocation, author names, timestamps and other data contained in images and documents.
- Threat monitoring: automated projects can blend OSINT with real-time alerts. For example, FBI Watchdog warns of legally seized domains and DNS changes in real time. There are also various tools that track criminal forums for early signs of ransomware campaigns.
Getting started with OSINT
If you’re starting from scratch, stick to the conventional intelligence cycle:
- Define your goals; in other words, be clear about what you’re investigating and what questions you’re seeking to answer.
- Identify relevant sources, such as social media, websites, government databases, or public records.
- Collect and analyze data with the help of select OSINT tools.
- Document what you find, and assess how reliable each nugget of information is. Make sure to source and rigorously document your findings so that you reduce errors and ensure your analysis is credible.
Recommended starter tools
If you’re just starting out, here are a few free tools with robust documentation:
- Explore the OSINT Framework to find categorized resources.
- Experiment with TheHarvester, SpiderFoot, and Recon-ng to understand automated data gathering.
- Learn basic Google Dorking and how to work with Shodan.
- Try Maltego, which integrates multiple APIs into one interface, to visualize relationships and datasets.
Mock case study
Let’s say a company suspects a data breach. An OSINT analyst might take these steps:
- They check breach databases such as Have I Been Pwned to see if company emails appear in known leaks.
- They also use Google Dorks to search for publicly exposed documents (e.g., “filetype:xls CEO email”)
- They scan for unprotected servers using Shodan or Censys.
- Using Maltego or social media intelligence (SocMINT) tools, they map employee social profiles tools to identify accidental exposure of confidential data.
- Ultimately, they discover that a server indexed by Google was using weak credentials. The team updates configurations and notifies users, preventing a potentially serious breach.
Parting thoughts
Knowing how to use OSINT tools is one thing; knowing how to investigate responsibly is another. Learn when to create sock puppet accounts for investigations, when to use scraping to handle large datasets, and when it’s appropriate to explore the dark web. Just remember never to lose sight of privacy laws and the ethics behind the search – they’re part of the craft.
We’re almost about to enter 2026, and open-source intelligence is more relevant than ever. it’s part of how cybersecurity, journalism, and research all operate. The explosion of available data, coupled with smarter automation and artificial intelligence, means that almost anyone can extract meaningful intelligence from open sources. Done right, OSINT turns the noise of the online world into actionable insights.