
CISA flagged a high-severity Ivanti Endpoint Manager (EPM) vulnerability as actively exploited in attacks and ordered U.S. federal agencies to patch systems within three weeks.
Ivanti’s EPM software is an all-in-one endpoint management solution for managing client devices across Windows, macOS, Linux, Chrome OS, and IoT platforms.
Tracked as CVE-2026-1603, this security flaw can be exploited by remote threat actors without privileges to bypass authentication and steal credential data in low-complexity cross-site scripting attacks that require no user interaction.
Ivanti patched the vulnerability one month ago, when it released Ivanti EPM 2024 SU5, which also addresses an SQL injection flaw that allows remote, authenticated attackers to read arbitrary data from the database.
While CISA has now tagged CVE-2026-1603 as exploited in the wild, Ivanti said it received no reports of exploitation when BleepingComputer reached out for confirmation on Monday.
“We are not aware of any customers being exploited by these vulnerabilities prior to public disclosure. These vulnerabilities were disclosed through our responsible disclosure program,” Ivanti says in the original advisory.
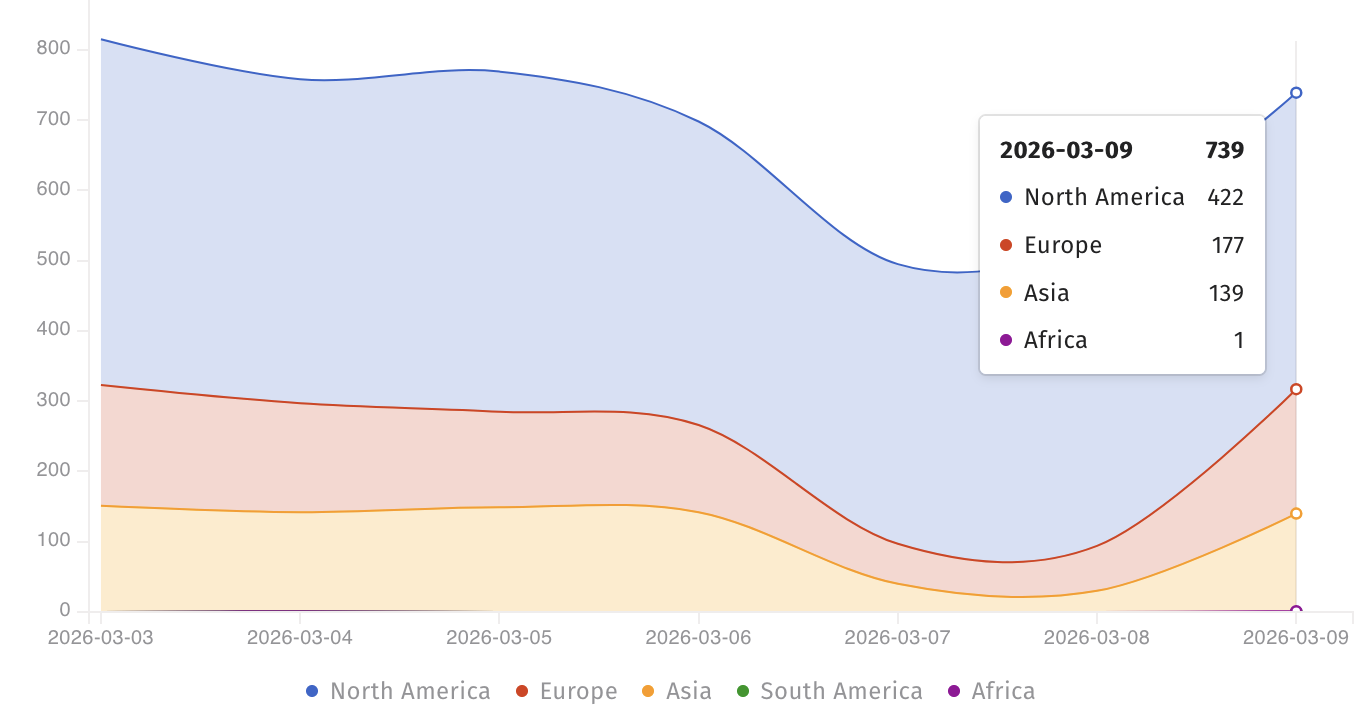
At the moment, the Shadowserver threat monitoring platform tracks over 700 Internet-facing Ivanti EPM instances, most of them in North America. However, there is no information on how many of them are still vulnerable to CVE-2026-1603 attacks.
Although it didn’t provide any details on attacks exploiting this flaw, CISA added it to its Known Exploited Vulnerabilities (KEV) Catalog on Monday, warning that such security bugs are “frequent attack vectors for malicious cyber actors and pose significant risks to the federal enterprise.”
The U.S. cybersecurity agency has also ordered Federal Civilian Executive Branch (FCEB) agencies to patch their systems within three weeks, by March 23, as mandated by a binding operational directive (BOD 22-01) issued in November 2021.
While Ivanti has yet to find evidence of active CVE-2026-1603 exploitation, threat actors often target Ivanti EPM vulnerabilities in attacks.
One year ago, CISA warned federal agencies to secure their networks against three other EPM flaws (CVE-2024-13159, CVE-2024-13160, and CVE-2024-13161) that were exploited in the wild.
CISA also ordered U.S. government agencies to patch another actively exploited EPM flaw (CVE-2024-29824) in October 2024.
Ivanti provides system and IT asset management products to more than 40,000 companies through a network of more than 7,000 partners worldwide.

