Building on the lessons learned in the Security Operations Center (SOC) at major events, we challenged ourselves to build something new at Cisco Live Amsterdam 2026, a closed-loop integration with Cisco XDR and Splunk Enterprise Security.
Planning a successful SOC begins with strong collaboration with the Network Operations Center (NOC). It also began with a focus, using the Splunk Security Maturity Methodology (S2M2).
The core missions of the SOC remain:
- Protect: Safeguard the network from threats and attacks, both internal and external
- Educate: Inform and engage attendees through SOC tours and blog content, and our white paper
- Innovate: Develop and implement new integrations, processes, workflows, and automations

Harnessing the Power of Splunk Security
A major goal for EMEA 2026 was breaking down the silos between “triage / investigating” and “threat hunting / incident response.”
By embedding Splunk Security Integration Engineers directly into the SOC, we curated specific workflows that allowed Tier 1 interns and Tier 2 analysts to perform complex investigations that were previously the domain of Tier 3 responders.
Configurations and other data were ready to go from previous events, including dashboards in Splunk, from the innovations for the National Football League Super Bowl LX SOC.
We refined the SOC Manager dashboard in Splunk from the experience at the Super Bowl SOC, showing the Incidents generated from detections in the security sources, and the status of the incidents, including escalations to Splunk Enterprise Security (ES).

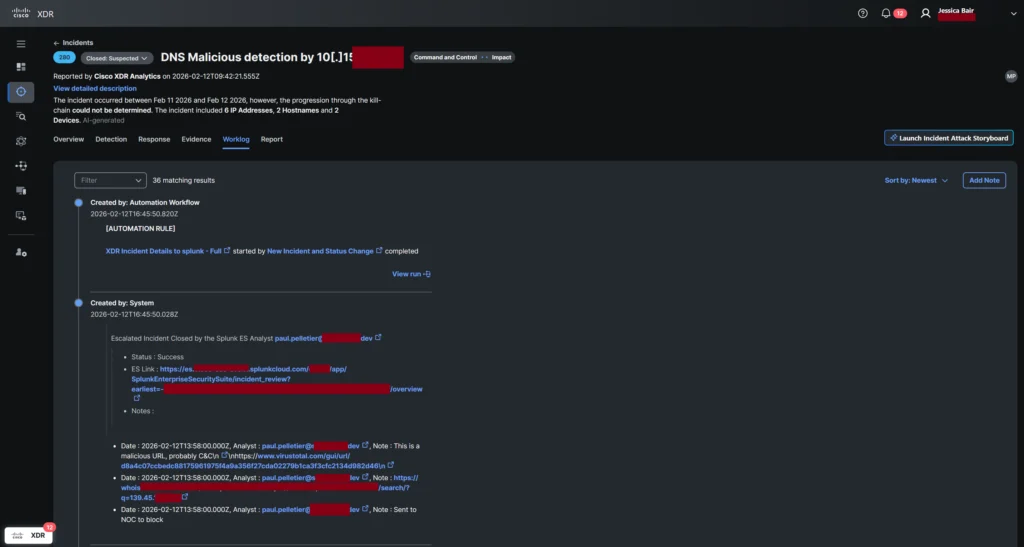
The Splunk Security Product Labs team worked to utilize the power of the Cisco XDR correlation engine, to bring Splunk ES Risk index logs as Sources into the XDR Data Analytics Platform. Those logs were correlated with other detections to produce Incidents for Triage and Investigation by Tier 1 /2 SOC analysts.

The integration between Cisco XDR and Splunk ES delivers a seamless experience for security operations teams by combining native XDR detections with Splunk’s extensive data backend and custom OCSF detections. Key innovations include:
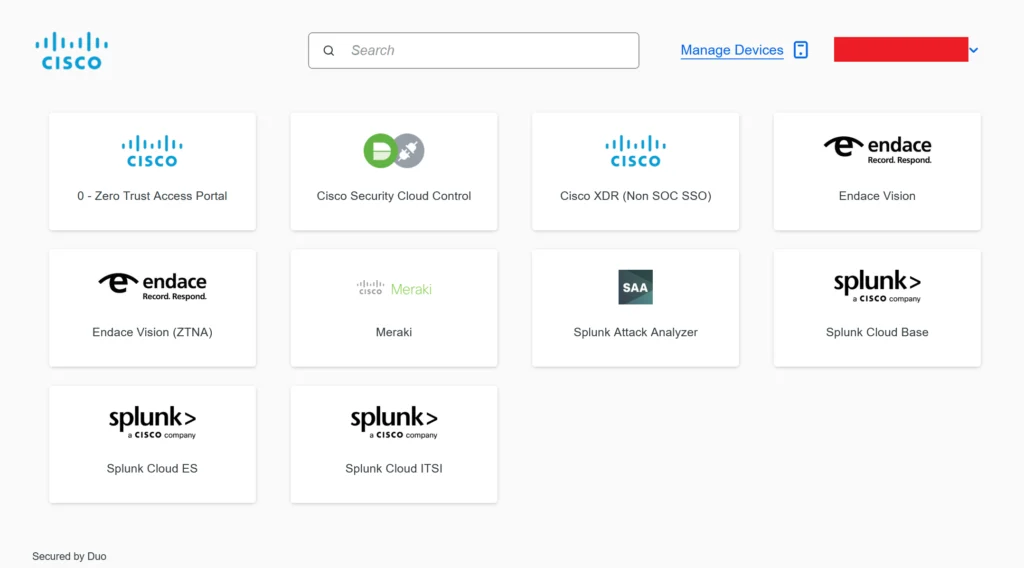
- Rapid Onboarding: New SOC analysts can be trained on XDR in under an hour, including integration pivot points with Splunk and Endace packet capture.
- Unified Incident Management: Detections from both Cisco XDR and Splunk were correlated within XDR, allowing analysts to see the source of detections in incidents, but maintaining a consistent user experience. This reduces the need for retraining before effectiveness in a mature SOC.
- Efficient Analyst Workflow: Tier 1/2 analysts triaged and investigated incidents in XDR, with the ability to pivot to Splunk logs and Endace packet data. When escalation is needed, enriched incident data is automatically sent to Splunk ES for Tier 3 analysts to continue investigations in Mission Control.
- Closed-Loop Automation: Incident status was automatically updated in XDR when the case was resolved in Splunk ES, closing the loop and ensuring synchronized records.
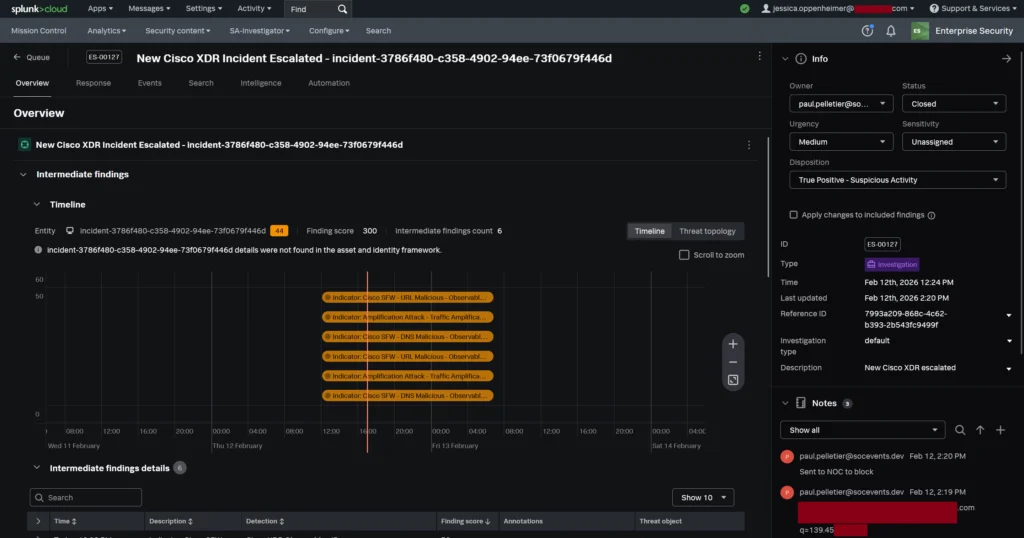
- Learning & Collaboration: Tier 1/2 analysts had role based access to Splunk ES via Duo Directory, empowering them to view the Tier 3 investigation notes and findings, and upleveling their skills.
- Openness & Customization: The integration leverages the open architecture of both Cisco XDR and Splunk, supporting custom detections and flexible workflows, as proven in high-profile SOC deployments.
This innovation enables security operations centers to maximize detection coverage, streamline incident response, reduce training overhead, and foster analyst growth, through tightly integrated, automated workflows.
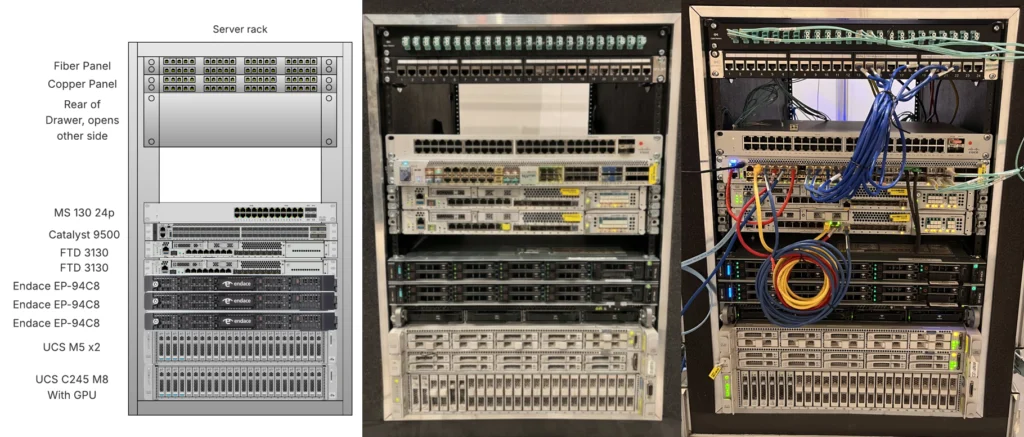
The Deployment: SOC in a Box
The SOC was successfully deployed in just 12 hours over 1 ½ days. This speed was not accidental; it was architectural. We utilized our portable “SOC in a Box”, a pre-configured hardware stack designed to be delivered in advance to the venue, connected to the NOC and immediately began producing actionable telemetry.
Key factors enabling this rapid setup included:
- Pre-validated Data Paths: Instant connectivity between the Cisco Live NOC, Splunk Enterprise Security and the Cisco Security Cloud.
- Battle-Tested Innovation: We integrated advanced security practices developed while safeguarding the Black Hat network, recognized as the world’s most hostile environment.
- Proven Workflows: We drew upon expertise and playbooks refined at the Super Bowl LX, RSAC, GovWare and prior Cisco Live SOCs.
The SOC Architecture: A “System of Systems”
The Amsterdam SOC was designed to overcome specific event constraints, such as the inability to install endpoint agents on attendee devices (BYOD) and the need to detect malware in encrypted traffic.
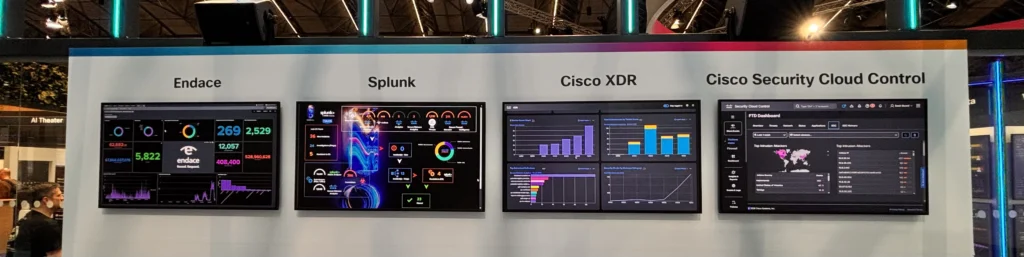
The Visibility Layer: The SOC team worked with the NOC to connect the ‘SOC in the Box’ and Cisco Secure Access for DNS security. We received a Switched Port Analyzer (SPAN) feed of network traffic.
The Investigation Layer: We deployed the EndaceProbe packet capture platform to record all network traffic. This allowed us to pivot from a Splunk alert directly to full packet capture (PCAP) to validate investigative hypotheses. Endace also generated Zeek logs for Splunk Enterprise Security (ES), while file content was reconstructed on the wire and streamed to Splunk Attack Analyzer and Cisco Secure Malware Analytics for sandboxing.
The Analysis & Identity Layer:
- Splunk Cloud and Splunk ES served as the SOC platform, aggregating risk scores and normalizing data into the Common Information Model (CIM).
- Cisco XDR acted as investigation visualization tool, using AI to confirm threats faster with Instant Attack Verification, enriched with threat intelligence provided by Cisco Talos, and licenses donated by alphaMountain, Pulsedive, and StealthMole, along with community sources.
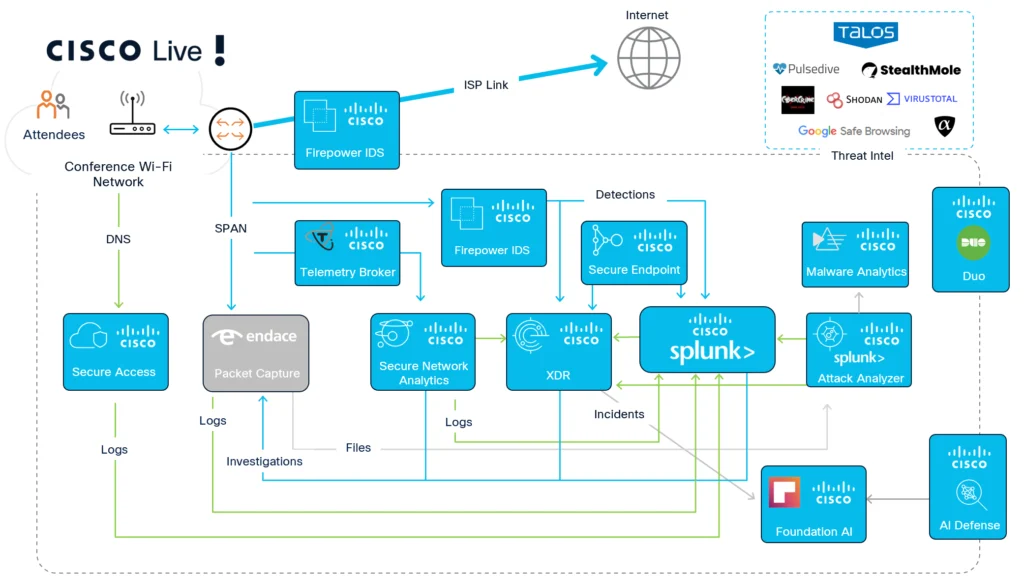
- Duo Directory and Identity Intelligence provided the identity plane, securing access to our tools via Single Sign-On and ensuring our analysts were authenticated and authorized within minutes of joining the shift.
The Statistics
Statistics are always a popular part of the SOC Tours. Below are the stats from this year’s event.
| Year | 2026 |
| Attendees (Cisco Live) | 21,000 |
| Total packets captured (Endace) | 130 billion |
| Total logs captured (Splunk) | 6.96 billion |
| Total sessions (Endace) | 911.3 million |
| Total unique devices (Endace in Splunk) | 32,434 |
| Total packets written to disk (Endace) | 120 TBs |
| Total logs written to cloud (Splunk) | 3.233 TBs |
| Peak bandwidth utilization (Endace) | 7 Gbps |
| DNS Requests (Cisco Secure Access) | 105 million / 29.3k blocked |
| Total clear text username/passwords (Endace) |
5,634 |
| Unique devices / accounts with clear text usernames / passwords (Endace) |
575 |
| Files sent for malware analysis (Endace) | – 1.7m file objects reconstructed by Endace. – 55,471 sent to Splunk Attack Analyzer – 45,514 sent to Secure Malware Analytics |

SOC Findings and Lessons Learned
The SOC team focuses on continuous innovation—the “OODA loop” of observing, orienting, deciding, and acting. We take time to document our experiences for the edification of the community.
Check out the deep-dive technical blogs below from the engineers who worked inside the SOC:
Acknowledgements
A heartfelt thank you to the engineers whose expertise made the first Cisco Live Amsterdam 2026 SOC a tremendous success.

Network Operations Center Liaisons
- Remco Kamerman, Luke Hebditch, Mark Bremner and Scott Neuman
Cisco Security and Splunk SOC Team
- SOC in a Box: Adi Sankar
- Splunk Security Integrations: Paul Pelletier and Kenneth Bouchard, with Josh Wilson and Duane Waddle
- Splunk Threat Researchers: Nasreddine Bencherchali and Paul Pang
- Breach Protection Suite: Mark Pleunes, Ibrahim Yusuf, Piotr Jarzynka, Matt Vander Horst, Yannis Steiakogiannakis and Eric Rennie, with Bilal Qamar
- User Protection Suite: Aaron Woland
- Firewall and Security Cloud Control: Adam Kilgore and Christopher Grabowski
Endace SOC Team
- Co-SOC Leader: Cary Wright Endace Engineering: Owen Gallagher, Sundarram Paravastu and Sam Brockelsby
We’d love to hear what you think! Ask a question and stay connected with Cisco Security on social media.
Cisco Security Social Media

